NSE4 | 100% Guarantee NSE4 Dumps Questions 2021
Act now and download your today! Do not waste time for the worthless tutorials. Download with real questions and answers and begin to learn with a classic professional.
Online Fortinet NSE4 free dumps demo Below:
NEW QUESTION 1
Review the IKE debug output for IPsec shown in the exhibit below.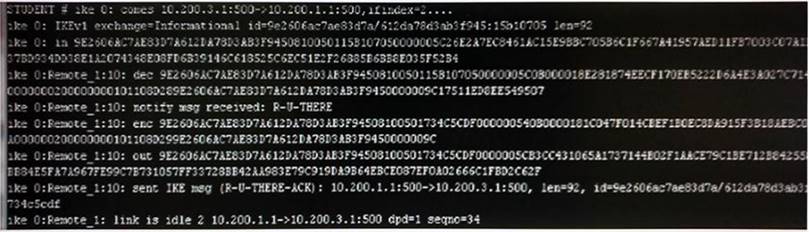
Which statements is correct regarding this output?
- A. The output is a phase 1 negotiation.
- B. The output is a phase 2 negotiation.
- C. The output captures the dead peer detection messages.
- D. The output captures the dead gateway detection packets.
Answer: C
NEW QUESTION 2
Review the IPsec diagnostics output of the command diagnose vpn tunnel list shown in the exhibit below.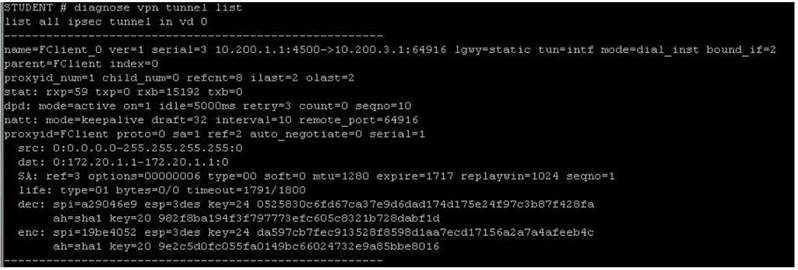
Which statements are correct regarding this output (Choose two.)
- A. The connecting client has been allocated address 172.20.1.1.
- B. In the Phase 1 settings, dead peer detection is enabled.
- C. The tunnel is idle.
- D. The connecting client has been allocated address 10.200.3.1.
Answer: AB
NEW QUESTION 3
Examine the following FortiGate web proxy configuration; then answer the question below:
config web-proxy explicit
set pac-file-server-status enable set pac-file-server-port 8080
set pac-file-name wpad.dat end
Assuming that the FortiGate proxy IP address is 10.10.1.1, which URL must an Internet browser use to download the PAC file?
- A. https://10.10.1.1:8080
- B. https://10.10.1.1:8080/wpad.dat
- C. http://10.10.1.1:8080/
- D. http://10.10.1.1:8080/wpad.dat
Answer: D
NEW QUESTION 4
Files reported as "suspicious" were subject to which Antivirus check"?
- A. Grayware
- B. Virus
- C. Sandbox
- D. Heuristic
Answer: D
NEW QUESTION 5
What are the ways FortiGate can monitor logs? (Choose three.)
- A. MIB
- B. SMS
- C. Alert Emails
- D. SNMP
- E. FortiAnalyzer
- F. Alert Message Console
Answer: CDF
NEW QUESTION 6
In a high availability cluster operating in active-active mode, which of the following correctly describes the path taken by the SYN packet of an HTTP session that is offloaded to a slave unit?
- A. Client - > slave FortiGate - > master FortiGate - > web server.
- B. Client - > slave FortiGate - > web server.
- C. Client - > master FortiGate - > slave FortiGate - > master FortiGate - >web server.
- D. Client - > master FortiGate - >slave FortiGate - > web server.
Answer: D
NEW QUESTION 7
Which are valid replies from a RADIUS server to an ACCESS-REQUEST packet from a FortiGate? (Choose two.)
- A. ACCESS-CHALLENGE
- B. ACCESS-RESTRICT
- C. ACCESS-PENDING
- D. ACCESS-REJECT
Answer: AD
NEW QUESTION 8
Which best describes the mechanism of a TCP SYN flood?
- A. The attackers keeps open many connections with slow data transmission so that other clients cannot start new connections.
- B. The attackers sends a packets designed to sync with the FortiGate
- C. The attacker sends a specially crafted malformed packet, intended to crash the target by exploiting its parser.
- D. The attacker starts many connections, but never acknowledges to fully form them.
Answer: D
NEW QUESTION 9
Which IP packets can be hardware-accelerated by a NP6 processor? (Choose two.)
- A. Fragmented packets.
- B. Multicast packet.
- C. SCTP packet.
- D. GRE packet.
Answer: BC
NEW QUESTION 10
Which profile could IPS engine use on an interface that is in sniffer mode? (Choose three)
- A. Antivirus (flow based
- B. Web filtering (PROXY BASED)
- C. Intrusion Protection
- D. Application Control
- E. Endpoint control
Answer: ABD
NEW QUESTION 11
A firewall policy has been configured for the internal email server to receive email from external parties through SMTP. Exhibits A and B show the antivirus and email filter profiles applied to this policy.
Exhibit A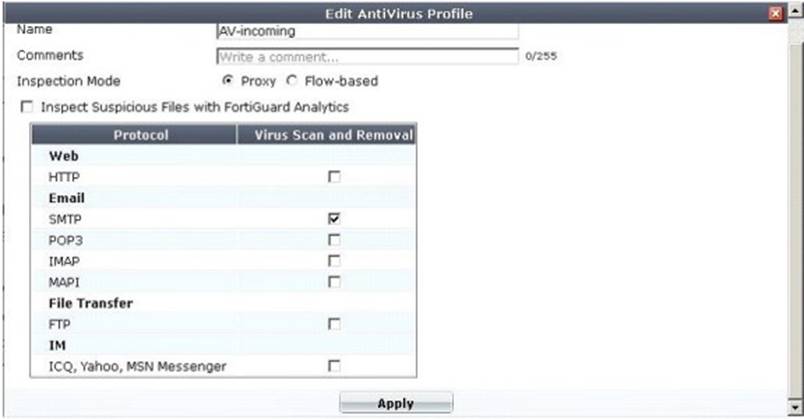
Exhibit B: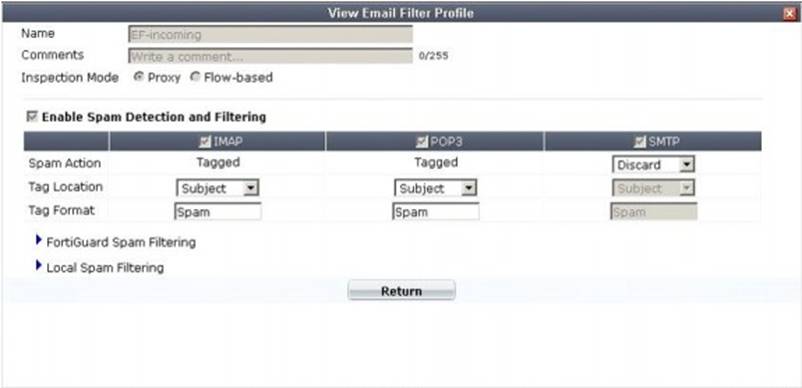
What is the correct behavior when the email attachment is detected as a virus by the FortiGate antivirus engine?
- A. The FortiGate unit will remove the infected file and deliver the email with a replacement message to alert the recipient that the original attachment was infected.
- B. The FortiGate unit will reject the infected email and the sender will receive a failed delivery message.
- C. The FortiGate unit will remove the infected file and add a replacement messag
- D. Both sender and recipient are notified that the infected file has been removed.
- E. The FortiGate unit will reject the infected email and notify the sender.
Answer: B
NEW QUESTION 12
If you have lost your password for the "admin" account on your FortiGate, how should you reset it?
- A. Log in with another administrator account that has "super_admin" profile permissions, then reset the password for the "admin" account.
- B. Reboot the FortiGat
- C. Via the local console, during the boot loader, use the menu to format the flash disk and reinstall the firmwar
- D. Then you can log in with the default password.
- E. Power off the FortiGat
- F. After several seconds, restart i
- G. Via the local console, within 30 seconds after booting has completed, log in as "maintainer" and enter the CLI commands to set the password for the "admin" account.
- H. Reboot the FortiGat
- I. Via the local console, during the boot loader, use the menu to log in as "maintainer" and enter the CLI commands to set the password for the "admin" account.
Answer: C
NEW QUESTION 13
Which of the following statements are true about Man-in-the-middle SSL Content Inspection? (Choose three.)
- A. The FortiGate device “re-signs” all the certificates coming from the HTTPS servers
- B. The FortiGate device acts as a sub-CA
- C. The local service certificate of the web server must be installed in the FortiGate device
- D. The FortiGate device does man-in-the-middle inspection.
- E. The required SSL Proxy certificate must first be requested to a public certificate authority (CA).
Answer: BCE
NEW QUESTION 14
What functions can the IPv6 Neighbor Discovery Protocol accomplish? (Choose two.)
- A. Negotiate the encryption parameters to use.
- B. Auto-adjust the MTU setting.
- C. Autoconfigure addresses and prefixes.
- D. Determine other nodes reachability.
Answer: CD
NEW QUESTION 15
Which of the following statements is true regarding a FortiGate device operating in transparent mode? (Choose three.)
- A. It acts as a layer 2 bridge
- B. It acts as a layer 3 router
- C. It forwards frames using the destination MAC address.
- D. It forwards packets using the destination IP address.
- E. It can perform content inspection (antivirus, web filtering, etc)
Answer: ACE
NEW QUESTION 16
Which statements are correct properties of a partial mesh VPN deployment. (Choose two.)
- A. VPN tunnels interconnect between every single location.
- B. VPN tunnels are not configured between every single location.
- C. Some location may be reachable via a hub location.
- D. There are no hub locations in a partial mesh.
Answer: BC
100% Valid and Newest Version NSE4 Questions & Answers shared by Surepassexam, Get Full Dumps HERE: https://www.surepassexam.com/NSE4-exam-dumps.html (New 301 Q&As)